Working Draft
Charter
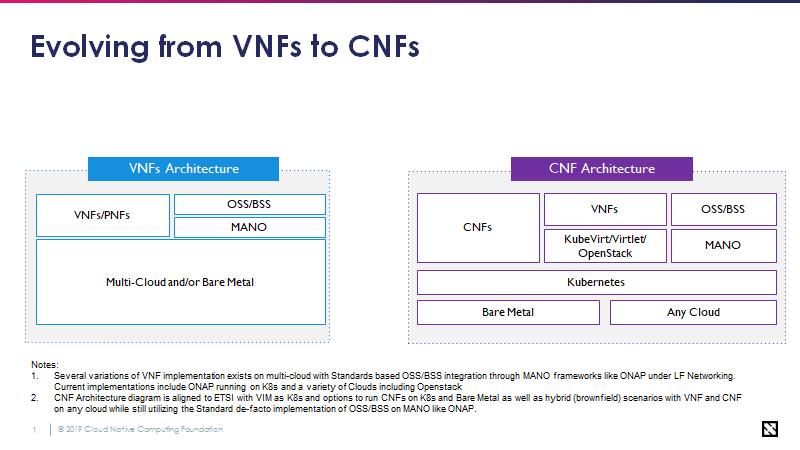
The OPNFV Verification Program Phase 2 (OVP 2.0) is an open source, community-led compliance and verification program to promote, enable, and evolve a thriving ecosystem of cloud-native telecoms where Cloud Native Network Functions (CNFs) from different vendors can inter-operate and run on the same immutable infrastructure. It includes CNF verification through publicly available CNF compliance test tooling based on requirements and tool-sets developed within OPNFV, ONAP and CNCF communities.
Source: LF Networking
Compliance & Verification Program
OVP2.0 E2E Compliance and Verification Program adds additional collaboration with the CNCF in the testing and verification of Cloud Native Network Functions.
Source: LF Networking
Verification and Certification Process
OPV 2.0 will provide an open source test suite which enables both open and closed source CNFs to demonstrate conformance and implementation of cloud-native practices. Compliance to the verification process will result in a LFN Cloud Native CNF badge(s). The LFN CNF badges should provide value for both operators and commercial vendors.
Cloud Native Network Function (CNF) Best Practices Criteria
(Propose that the below should be aligned, agreed, and later decomposed into testable items. We should sort with mandatory first and optional (but still verifiable) criteria at the end.
CNF Best Practice Criteria | |
1 | CNFs are decomposed into loosely coupled collection of services (e.g. use micro-services design). |
2 | Micro-services should, where possible, be independent of the host operating system. |
3 | Micro-services should utilize well defined declarative APIs |
4 | Micro-services should be designed with a clean separation between stateful and stateless services (have separation of state storage and business logic) |
5 | Clear separation should exist between micro-services (e.g. use of containers) |
6 | Micro-services should provide a mechanism to verify container content. Containers should not require root level permissions. It should be possible to secure API access to a micro-service using common methods. |
7 | Micro-services should be resilient (self-healing and distributed)
|
8 | Micro-services should be elastic (vertical and horizontal scaling in response to load)
|
9 | Micro-services should be dynamic - where possible, have a small footprint and fast startup time enabling efficient use of resources and rapid scaling. |
10 | Micro-services may utilize a service mesh for service-to-service communication over a network |
11 | Micro-service/Container life-cycle is managed by an orchestrator (e.g. K8s) |
12 | Micro-services utilize immutable infrastructure: |
A |
|
B |
|
C |
|
D |
|
E |
|
F |
|